Substitution Techniques
Er. Shivam Singh
Substitution Techniques in Cryptography
Substitution techniques are one of the foundational methods in cryptography, used to secure information by replacing elements of the plaintext (original message) with other elements. This replacement is governed by a specific set of rules or algorithms, known as a cipher. Substitution techniques date back thousands of years and have played a crucial role in the development of modern cryptographic systems.
This article explores substitution techniques, their types, historical significance, advantages, limitations, and their relevance in today's cryptographic landscape.
What Are Substitution Techniques?
Substitution techniques replace characters or groups of characters in the plaintext with other characters or symbols to produce ciphertext (encrypted message). The primary goal is to obscure the original message so that it becomes unintelligible without the decryption key.
The simplest form of substitution is the monoalphabetic substitution, where each character in the plaintext is substituted with a corresponding character from a fixed substitution alphabet.
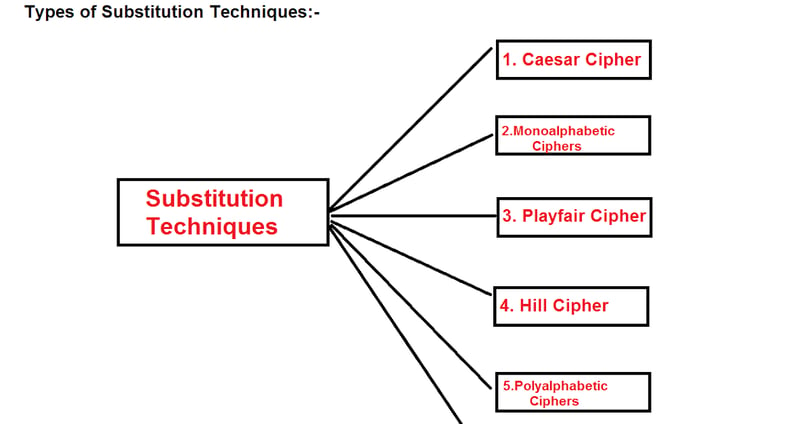
Types of Substitution Techniques
Substitution techniques can be broadly classified into two main types: monoalphabetic and polyalphabetic substitutions.
1. Monoalphabetic Substitution
In monoalphabetic substitution, each character in the plaintext is substituted with a fixed corresponding character from a substitution alphabet. The relationship between the plaintext and ciphertext characters is one-to-one and does not change throughout the message.
Caesar Cipher: One of the earliest and simplest substitution ciphers, attributed to Julius Caesar. It shifts each character in the plaintext by a fixed number of places in the alphabet.
Example: With a shift of 3, "HELLO" becomes "KHOOR."
Atbash Cipher: A monoalphabetic substitution cipher where the alphabet is reversed. The first letter is substituted with the last, the second with the second last, and so on.
Example: "HELLO" becomes "SVOOL."
Simple Substitution Cipher: A general form where each letter in the plaintext is replaced with a unique character based on a predefined key.
Example: Using the key "QWERTYUIOPASDFGHJKLZXCVBNM," "HELLO" becomes "ITSSG."
2. Polyalphabetic Substitution
In polyalphabetic substitution, multiple substitution alphabets are used. The relationship between plaintext and ciphertext characters changes based on their position in the text. This technique reduces the frequency analysis vulnerabilities of monoalphabetic ciphers.
Vigenère Cipher: A polyalphabetic cipher that uses a keyword to determine which substitution alphabet to use for each character.
Example: Using the keyword "KEY," the plaintext "HELLO" is encrypted as:
H (shift by K) → R
E (shift by E) → I
L (shift by Y) → J
Result: "RIJVS."
Playfair Cipher: A digraph substitution cipher that encrypts pairs of letters using a 5x5 grid of alphabets generated by a keyword. It avoids single-letter substitution and enhances security.
Hill Cipher: Uses linear algebra and matrix multiplication for substitution. A matrix key is used to transform plaintext into ciphertext.
Historical Significance of Substitution Techniques
Substitution techniques have been used for centuries to secure messages, especially during wars and political conflicts. For example:
The Caesar Cipher was used by Julius Caesar to communicate with his generals.
The Atbash Cipher was used in Hebrew texts.
The Vigenère Cipher, known as "le chiffre indéchiffrable" (the unbreakable cipher), remained unbroken for centuries until the 19th century.
While substitution techniques were effective in ancient times, advancements in cryptanalysis eventually exposed their vulnerabilities.
Advantages of Substitution Techniques
Simplicity: Substitution ciphers are straightforward to understand and implement, making them ideal for teaching cryptographic principles.
Speed: Encryption and decryption processes are computationally efficient, especially for monoalphabetic ciphers.
Foundation for Modern Ciphers: Many modern cryptographic algorithms, such as the Advanced Encryption Standard (AES), incorporate substitution principles within their design.
Limitations of Substitution Techniques
Vulnerability to Frequency Analysis:
Monoalphabetic substitution ciphers are highly susceptible to frequency analysis because certain letters (e.g., 'E' in English) occur more frequently than others. Analyzing the frequency of letters in the ciphertext can reveal the substitution pattern.
Limited Security:
The fixed substitution patterns of monoalphabetic ciphers make them easy to break with modern computational tools.
Key Management Challenges:
Complex substitution systems, like polyalphabetic ciphers, require the secure management and distribution of keys, which can be cumbersome.
Scalability:
Substitution techniques are not suitable for encrypting large amounts of data or for use in dynamic systems where keys need frequent updates.
Modern Relevance of Substitution Techniques
While classical substitution techniques are no longer used for secure communication, their principles have influenced modern cryptography. Substitution techniques are now implemented in more sophisticated forms within modern encryption algorithms:
Advanced Encryption Standard (AES): AES employs substitution boxes (S-boxes) to perform byte-level substitution as part of its encryption process.
Data Encryption Standard (DES): DES also incorporates substitution as one of its primary operations.
Substitution techniques are still used in lightweight cryptography for resource-constrained environments like IoT devices, where computational efficiency is critical.
Conclusion
Substitution techniques are a cornerstone of classical cryptography and have significantly influenced the evolution of secure communication methods. While their standalone use has been rendered obsolete by modern cryptanalysis, their principles remain integral to contemporary encryption algorithms.
From the simplicity of the Caesar Cipher to the complexity of the Vigenère Cipher, substitution techniques demonstrate how creativity and mathematics can protect sensitive information. Understanding these techniques not only provides insight into the history of cryptography but also lays the foundation for appreciating the sophistication of modern encryption systems.
© Copyright 2025 Skytpoint . All Rights Reserved.