The OSI security architecture
Discover the fundamentals of the OSI Security Architecture, its layers, and protocols in network security. Learn how the OSI model enhances data protection and secures communications across networks. Perfect for cybersecurity professionals and students. Dive into real-world applications and best practices!
CRYPTOGRAPHY AND COMPUTER NETWORKS
Er. Shivam Singh
The OSI Security Architecture: A Comprehensive Overview
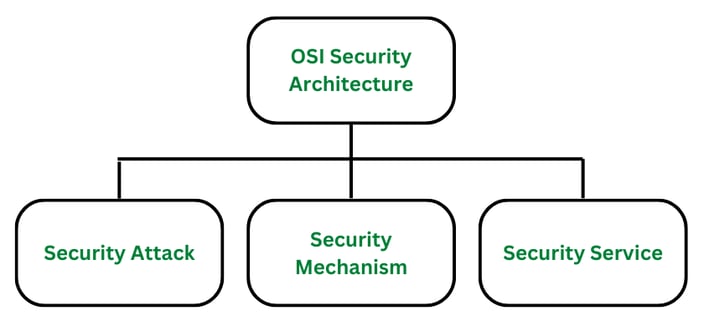
In the digital age, securing networks and communication systems is paramount. One of the most fundamental frameworks for understanding network security is the OSI (Open Systems Interconnection) security architecture. Developed by the International Organization for Standardization (ISO), the OSI model provides a layered approach to network communication. While the OSI model itself focuses on facilitating communication between different systems, the OSI security architecture is an extension that highlights the security mechanisms required to safeguard these communications.
This architecture serves as a blueprint for building secure communication systems, ensuring confidentiality, integrity, and availability of data. Understanding the OSI security architecture helps organizations and developers design networks with robust security measures. This article delves into the OSI security architecture, discussing its structure, the types of security mechanisms it provides, and its significance in today’s digital world.
The OSI Model: A Quick Recap
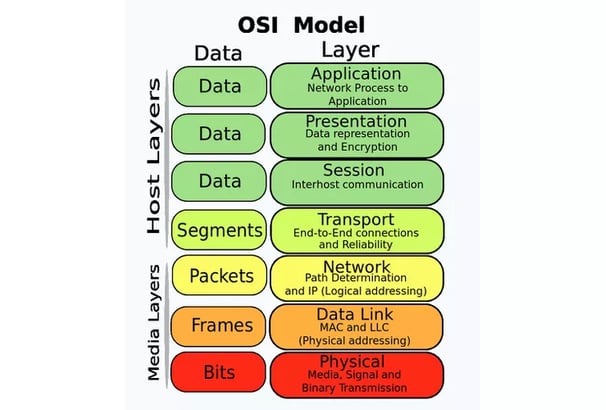
The OSI model consists of seven layers, each of which serves a specific function in the communication process:
Physical Layer: Deals with the physical connection between devices.
Data Link Layer: Responsible for error-free data transmission between two directly connected nodes.
Network Layer: Manages routing and forwarding of data.
Transport Layer: Ensures complete data transfer with error detection and recovery.
Session Layer: Manages sessions and connections between applications.
Presentation Layer: Translates data between the application and network format.
Application Layer: Interfaces with the user and provides network services.
These layers function in a hierarchical manner, with each layer relying on the functionalities of the one below it. The OSI security architecture takes this layered approach and applies security measures across the layers to protect data at each point in the communication process.
Real-world applications of number theory services extend beyond traditional data security. They are integral in protocols such as Transport Layer Security (TLS) and Secure Sockets Layer (SSL), which provide secure communication over computer networks. These protocols utilize cryptographic techniques underpinned by number theory to ensure confidentiality, integrity, and authentication, establishing a trustworthy environment for data exchange.
Mechanisms of OSI Security: Implementing Number Theory
The OSI Security Architecture utilizes several mechanisms to incorporate number theory in its various protocols, thereby enhancing the security of information systems. One of the most prominent applications of number theory in OSI Security is through cryptographic algorithms. Among these, the RSA algorithm stands out due to its reliance on the properties of large prime numbers. RSA employs two keys: a public key for encryption and a private key for decryption, which ensures a secure communication channel. The mathematical challenge of factoring large composite numbers lends significant strength to RSA's security model.
Another essential mechanism that leverages number theory is the Diffie-Hellman key exchange protocol. It allows two parties to securely generate a shared secret key over an insecure channel. This is achieved through the difficulty of calculating discrete logarithms, a problem that underpins the algorithm. By exchanging public values based on chosen private keys, the participants can compute the same shared secret without revealing their respective private keys, thereby maintaining confidentiality and integrity in communications.
Furthermore, elliptic curve cryptography (ECC) provides another robust mechanism. ECC operates on the complexities of elliptic curves over finite fields, enabling secure and efficient cryptographic operations. The smaller key sizes required for equivalent security levels make ECC particularly valuable for resource-constrained devices, making it a preferred choice in modern applications.
Key management plays a crucial role within these mechanisms. It involves the generation, distribution, and storage of cryptographic keys, essential for maintaining the security of encrypted information. Secure key exchange protocols ensure that keys are shared in a manner that is resilient against potential interception or compromise. The effectiveness of number theory services in OSI security largely hinges on these robust mechanisms, facilitating secure communication and safeguarding critical data across networks.
Attacks on OSI Security: Vulnerabilities and Countermeasures
The OSI Security Architecture, while designed to protect data integrity and confidentiality, is susceptible to various attacks that exploit weaknesses within its frameworks. One prevalent method is the brute force attack, where an attacker systematically attempts every possible combination to crack encryption keys. This approach leverages the predictable nature of some key generation algorithms, specifically those reliant on inadequate number theory services. To mitigate this threat, organizations should implement stronger key lengths, ensuring they exceed the computational capabilities of the attackers.
Another notable threat is the man-in-the-middle attack. In this scenario, the attacker intercepts and potentially alters communications between two parties who believe they are directly communicating with each other. This attack typically exploits vulnerabilities in authentication protocols. To counteract this, it is recommended to use robust encryption methods, alongside digital certificates to authenticate identities and secure connections. Regular training for employees regarding phishing and social engineering tactics can further bolster defenses against these interception techniques.
Additionally, mathematical attacks on cryptographic algorithms pose significant risks. These attacks exploit weaknesses in the underlying mathematical structures that form the basis of the encryption protocols. For example, attacks targeting specific algorithms like RSA or ECC can render these systems ineffective if vulnerabilities are not promptly addressed. It is crucial to regularly review and update cryptographic algorithms while remaining vigilant for any emerging threats that could signal potential weaknesses.
In practice, organizations must stay proactive by routinely updating security measures and adopting best practices, such as multi-factor authentication and frequent security audits. By comprehensively understanding the potential vulnerabilities in OSI Security and the corresponding countermeasures, entities can significantly enhance their capabilities to protect sensitive information during network communications.
© Copyright 2025 Skytpoint . All Rights Reserved.