Network Security Model
The network security model plays a crucial role in safeguarding the integrity, confidentiality, and availability of data in a network. By understanding how it works and implementing the right security measures, both individuals and organizations can protect their valuable information from attackers.
CRYPTOGRAPHY AND COMPUTER NETWORKS
Er. Shivam Singh
Network Security Model: A Simple Guide
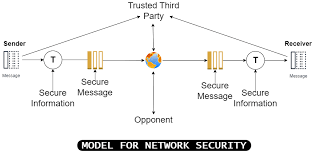
In today’s world, where everything is connected through the internet, ensuring the safety and privacy of information while it travels from one place to another is essential. This is where network security comes into play. It refers to the measures and practices used to protect the network, its data, and its services from unauthorized access, misuse, or attacks. The network security model helps us understand how to safeguard these elements. Let’s explore it in simple terms.
Components of a Network Security Model
A network security model includes various components that work together to protect data. The key elements include:
Sender (Source): The sender is the person, device, or software that is sending the data. For example, if you’re sending an email to your friend, you are the sender.
Receiver (Destination): The receiver is the person, device, or software that is intended to get the data. In the email example, your friend is the receiver.
Message (Data): The message is the actual information or data being transferred from the sender to the receiver. This could be anything like an email, a video, or sensitive financial information.
Transmission Medium: This is the path through which the message travels from the sender to the receiver. It could be a physical medium, such as cables or wireless signals like Wi-Fi.
Security Mechanisms: These are the technologies and practices put in place to secure the data. This includes encryption, firewalls, intrusion detection systems (IDS), etc.
Security Attacks: These are attempts by hackers or unauthorized entities to steal or damage data. Common types of attacks include phishing, denial of service (DoS), and man-in-the-middle (MitM) attacks.
Security Services: These are the functions provided by the security mechanisms to protect data. Examples include confidentiality, integrity, authentication, and non-repudiation.
How Does the Network Security Model Work?
Now that we know the key components, let’s look at how the network security model works. The process typically follows these steps:
Sender Prepares the Message: The sender first prepares the data they want to send. This message could be anything from a file transfer to sending a sensitive password over the network.
Encryption: Before the message is sent, it is often encrypted to ensure security. Encryption is the process of converting the original data into a coded format so that unauthorized people cannot understand it. Only the authorized receiver has the key to decode (or decrypt) the message.
Transmission through Medium: The encrypted message then travels through the network via the transmission medium, which could be cables (like Ethernet cables) or wireless signals (like Wi-Fi).
Security Checks: During the transmission, various security mechanisms are in place to ensure the data remains safe. Firewalls may check if the incoming or outgoing traffic is secure. Intrusion detection systems (IDS) monitor the network to detect any suspicious activity or potential attacks.
Decryption by Receiver: Once the message reaches the receiver, it is decrypted (i.e., converted back to its original form). Only the intended receiver should have the correct key to unlock this message. This ensures that even if a hacker intercepts the data, they cannot read it without the decryption key.
Authentication: Along with encryption, authentication is used to verify that the sender and receiver are legitimate. Authentication mechanisms like passwords, digital certificates, or two-factor authentication help confirm that the person or device sending or receiving the message is genuine.
Message Delivery: After these security measures, the message safely reaches the receiver. If any part of the message is tampered with or intercepted, security mechanisms like integrity checks will detect the issue and inform the sender or receiver about the breach.
Common Security Mechanisms
Encryption: Encryption ensures that even if a hacker manages to intercept the data, they cannot understand it without the correct decryption key. Two main types of encryption are symmetric and asymmetric encryption. Symmetric encryption uses one key for both encryption and decryption, while asymmetric encryption uses two keys – one for encryption (public key) and one for decryption (private key).
Firewalls: A firewall is like a gatekeeper that monitors incoming and outgoing traffic on the network. It blocks or allows data based on pre-set security rules. For example, it can block data from suspicious websites or unauthorized users.
Intrusion Detection System (IDS): An IDS monitors the network for unusual or suspicious activity, such as hacking attempts or malware. If it detects something suspicious, it can alert the system administrator or automatically block the activity.
Digital Signatures: Digital signatures are like electronic fingerprints. They are used to verify the authenticity of the sender and ensure that the message has not been altered during transmission. This adds an extra layer of trust in communication.
Virtual Private Networks (VPNs): VPNs allow users to send and receive data over a secure, encrypted connection, even on public networks. VPNs are commonly used by businesses to allow remote employees to securely access the company’s network.
Antivirus and Anti-malware Software: Antivirus software helps detect and remove malicious software like viruses, worms, or trojans. It is essential to keep this software updated to protect against the latest threats.
Types of Security Attacks
While the network security model is designed to protect data, attackers continually develop new ways to breach systems. Some common types of attacks include:
Phishing: Phishing is when attackers try to trick users into giving up sensitive information like passwords or credit card numbers by pretending to be a trusted entity.
Denial of Service (DoS): A DoS attack aims to overload a network or server with too much traffic, causing it to crash or become unavailable.
Man-in-the-Middle (MitM): In a MitM attack, a hacker intercepts communication between two parties to steal or alter the data being transferred.
Ransomware: Ransomware is malicious software that locks users out of their data or systems until a ransom is paid.
© Copyright 2025 Skytpoint . All Rights Reserved.